27 December 2019
The 18th and 24th of December 2019, the website of the Afghani Daily Newspaper Etilaat Roz (etilaatroz.com) received two denial of service attacks. Etilaat Roz was created in 2012 in Afghanistan, as new media platform funded by a group of young people working towards a better Afghanistan. Etilaat Roz is known to deliver investigative reports about corruption in the country.
Two days before the cyberattacks started, the Etilaat Roz Daily published two investigative reports:
- “How was the budget of Code 91 spent in 1397?” The story, considered as one of the major and most important investigative reports in the history of Afghan investigative journalism, shows how the Afghan government has manipulated the National Budget. More can be read in English here.
- Has Hanif Daneshyar forged membership in the Election Commission? The second report examines the identity documents of a member of the IEC (Afghanistan’s Independent Election Commission) and shows the forgery of his ID card to become eligible and secure his current position at IEC. English translation is available here: https://kabulnow.af/2019/12/iec-commissioner-danishyar-committs-age-fabrication/
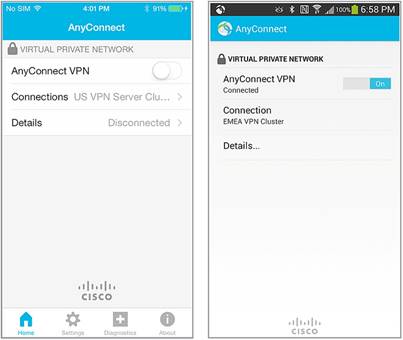
Cisco Anyconnect VPN to hide

An analysis of the traffic reveals that the attacker selected the URL to target (index.php) before the attack using two VPN services: PureVPN and Cisco Anyconnnect. The attacker changed IP address frequently, all the IPs belong to Cisco VPN service.
23.237.86{.}133 US
109.202.106{.}85 NL
89.187.177{.}111 US
89.187.177{.}112 US
89.187.177{.}81 US
89.187.177{.}66 US
The attacker used the Cisco US and NL Cluster “cisadd2.com” hosted
PureVPN and Voxility fake the location of their VPN service
During the review of the traffic of the attacker, we found also one interesting IP belonging to PureVPN service: 172.111.208{.}68
The IP according to the whois database is allocated to Afghanistan.
etName: INTERNET-SECURITY-15-VOXILITY-AF
NetHandle: NET-172-111-208-0-1
Parent: INTERNET-SECURITY-15 (NET-172-111-128-0-1)
NetType: Reassigned
OriginAS: AS3223
Organization: VOXILITY-AF (VOXIL-11)
RegDate: 2017-07-19
Updated: 2017-07-19
Ref: https://rdap.arin.net/registry/ip/172.111.208.0
OrgName: VOXILITY-AF
OrgId: VOXIL-11
Address: Shashdarak 2nd
Address: 1002 Kabul
Address: Kabul, Afghanistan
City: Kabul
The IP range is registered in the whois database to the address Shashdarak 2nd in 1002 Kabul that matches the address of the ACG Data Center in Kabul.

However, after a few routing tests, we determined that the IP range was in fact located in Los Angeles, connected to the Equinix Internet Exchange inside of Voxility infrastructure.

Since 2015, PureVPN announces that they have a VPN a service in Afghanistan when in fact the service is located in the US. Two IPs are advertised as being in Afghanistan.
vlus-af-ovpn-tcp.pointtoserver.com 172.111.208{.}2
vlus-af.pointtoserver.com 206.123.150{.}62
The first one is 172.111.208{.}2 is in Los Angles and the second 206.123.150{.}62 is located in Chicago

Their fake information is so obvious that they even confuse Afghanistan with Mongolia in their website.

Conclusions
After reviewing the forensics information of the attacks against Etilaat Roz, we confirmed the following:
- The attacks were targeted and connected to the release of their recent investigatory reports.
- The attacker used two VPN services to hide its location: Cisco Anyconnect and PureVPN
- PureVPN and Voxility provide fake information about the location of their VPN service in Afghanistan.
